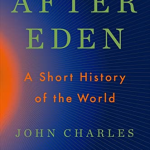
After Eden: A short history of the world by John Charles Chasteen
A history of the world but from the point of view of how society organises and people treat each other. Interesting 3/5
Ground Combat: Puncturing the Myths of Modern War by Ben Connable
A bit dry and academic with a lot of “talking to my dataset” but some interesting bits on trends in modern warfare including early parts of Ukraine war. 3/5
Breakneck: China’s Quest to Engineer the Future by Dan Wang
Contrasts the Lawyer Culture of the US vs China’s Engineer Culture. Discusses aspects of China’s culture, Government and Industry. Recommend 4/5
The Devil Reached towards the Sky: An Oral History of the Making and Unleashing of the Atomic Bomb by Garrett M. Graff
Structured as quotes from characters delivered by actors. Better coverage of Oak Ridge and Hanford than most books. Pretty good 4/5
My Audiobook Scoring System
- 5/5 = Brilliant, top 5 book of the year
- 4/5 = Above average, strongly recommend
- 3/5 = Average. in the middle 70% of books I read
- 2/5 = Disappointing
- 1/5 = Did not like at all